DoT Explained
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
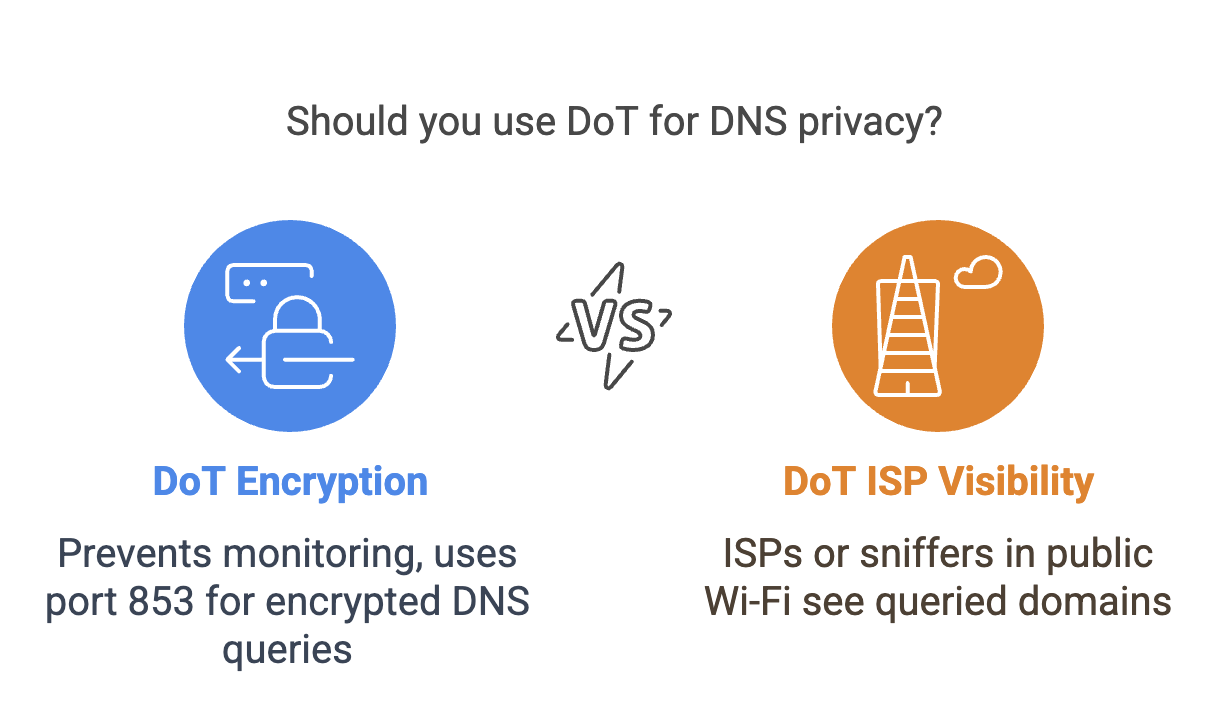
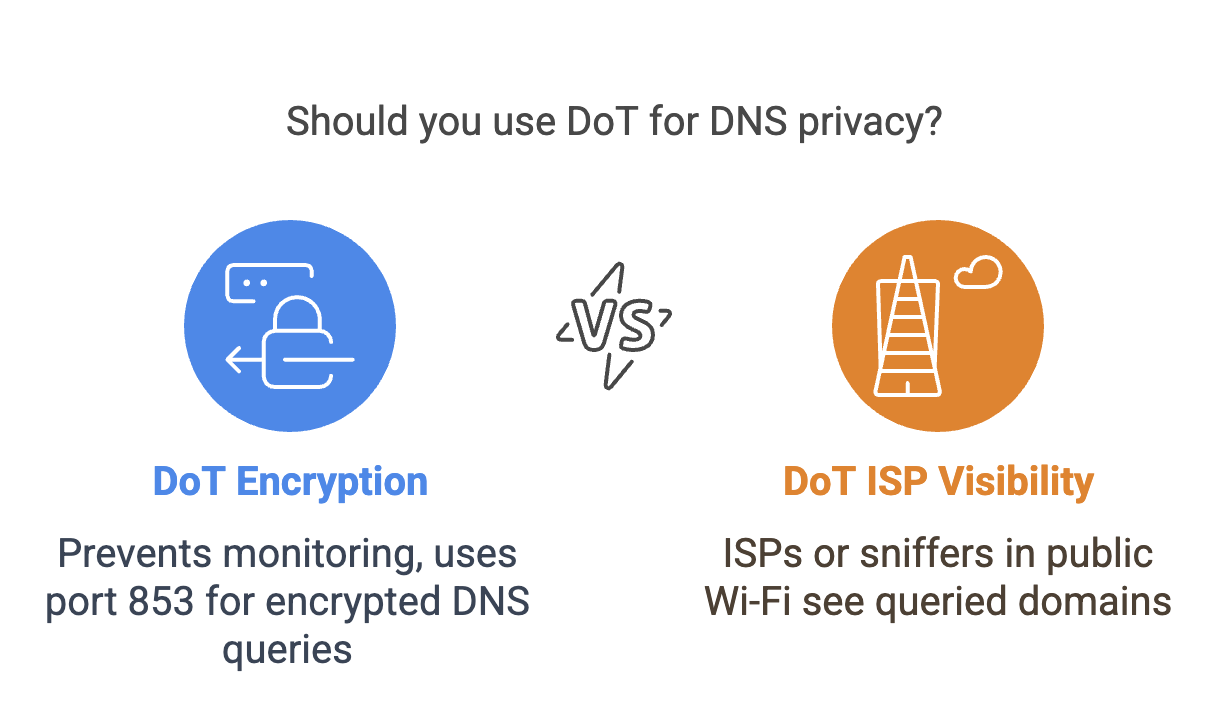
DNS over TLS (DoT) encrypts DNS queries using the Transport Layer Security (TLS) protocol. Instead of sending DNS queries in clear text over UDP port 53, the client establishes a secure TLS session with the DNS resolver and sends queries through that encrypted channel.
This prevents intermediaries such as Internet Service Providers, network administrators, or attackers on public Wi-Fi networks from inspecting or modifying DNS queries in transit. Without encryption, traditional DNS queries reveal every domain a user looks up.
The dig utility can test DNS over TLS using the +tls option.
The following example queries the ietf.org domain using an encrypted DNS session.
dig @1.1.1.1 ietf.org A +tls
In this case, the DNS query is transmitted through a TLS-encrypted connection instead of standard DNS over UDP.
Traditional DNS traffic is unencrypted and exposes browsing activity to network observers. DoT improves privacy by encrypting DNS queries while still maintaining compatibility with existing DNS infrastructure.
However, although DoT encrypts DNS traffic, the destination resolver remains visible, and traffic analysis may still reveal patterns of DNS activity.