DoH Explained
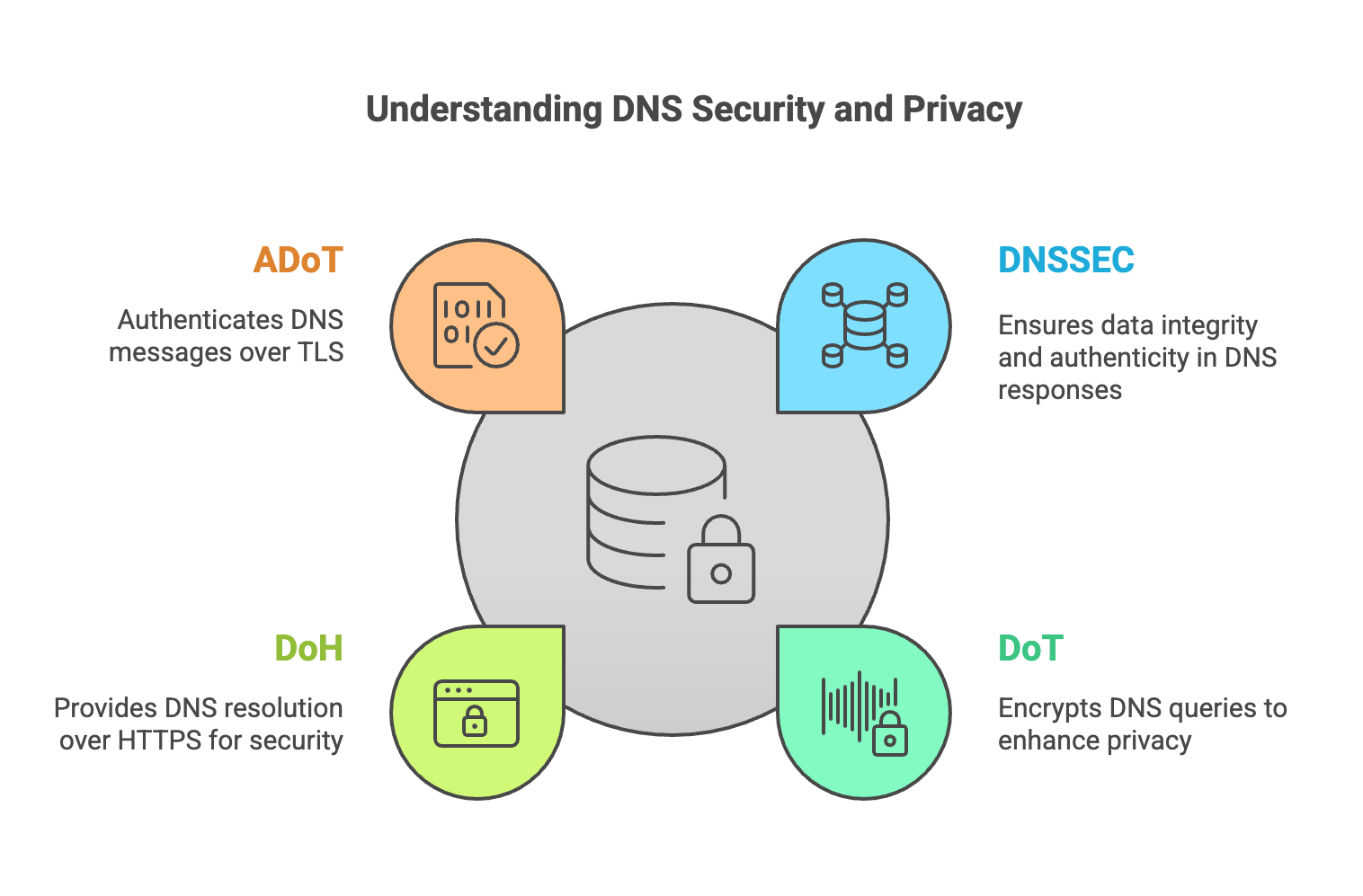
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
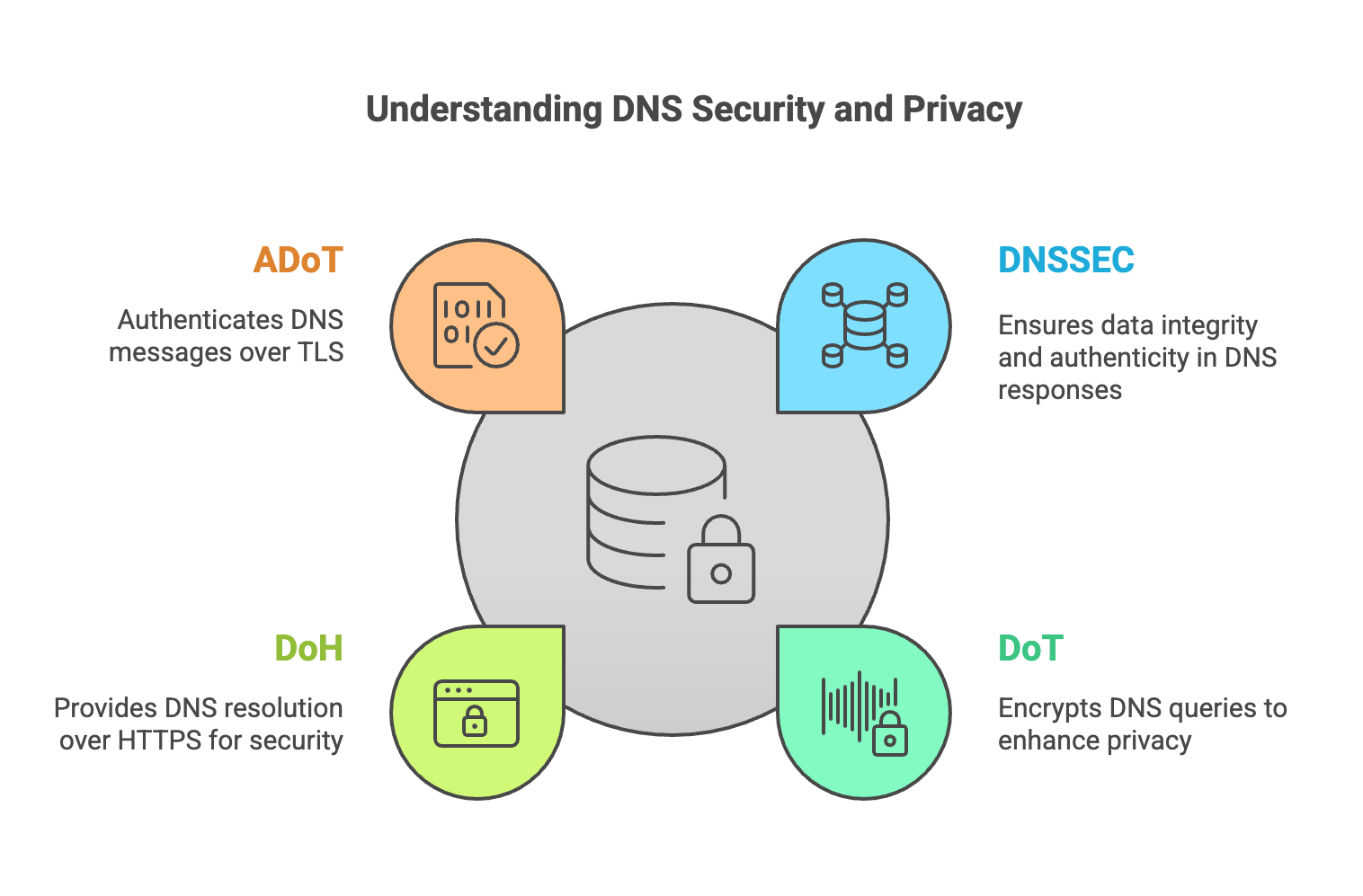
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
DNS over HTTPS (DoH) encrypts DNS queries using the HTTPS protocol. Instead of sending DNS traffic directly to a resolver over port 53 or 853, the DNS query is encapsulated inside an HTTPS request and transmitted over TCP port 443.
Because DoH traffic is indistinguishable from normal web traffic, it can bypass network controls that traditionally monitor or filter DNS traffic. This makes DoH attractive for privacy-focused applications, but it can also complicate network security monitoring.
Some DNS utilities can query DoH resolvers directly. For example:
curl -H 'accept: application/dns-json' \
'https://cloudflare-dns.com/dns-query?name=ietf.org&type=A'
This sends a DNS query using an HTTPS request and returns the DNS response encoded in JSON.
While DoH improves user privacy by encrypting DNS traffic, it can also reduce visibility for enterprise security tools and Protective DNS systems that rely on observing DNS queries.
For this reason, many enterprise and ISP networks prefer DNS over TLS (DoT) because it encrypts DNS traffic while keeping DNS traffic identifiable and easier to manage.