What is DNS Cache Poisoning?
DNS cache poisoning is an attack that manipulates DNS resolvers by inserting false records into their cache, redirecting users to malicious destinations.
DNS cache poisoning is an attack that manipulates DNS resolvers by inserting false records into their cache, redirecting users to malicious destinations.
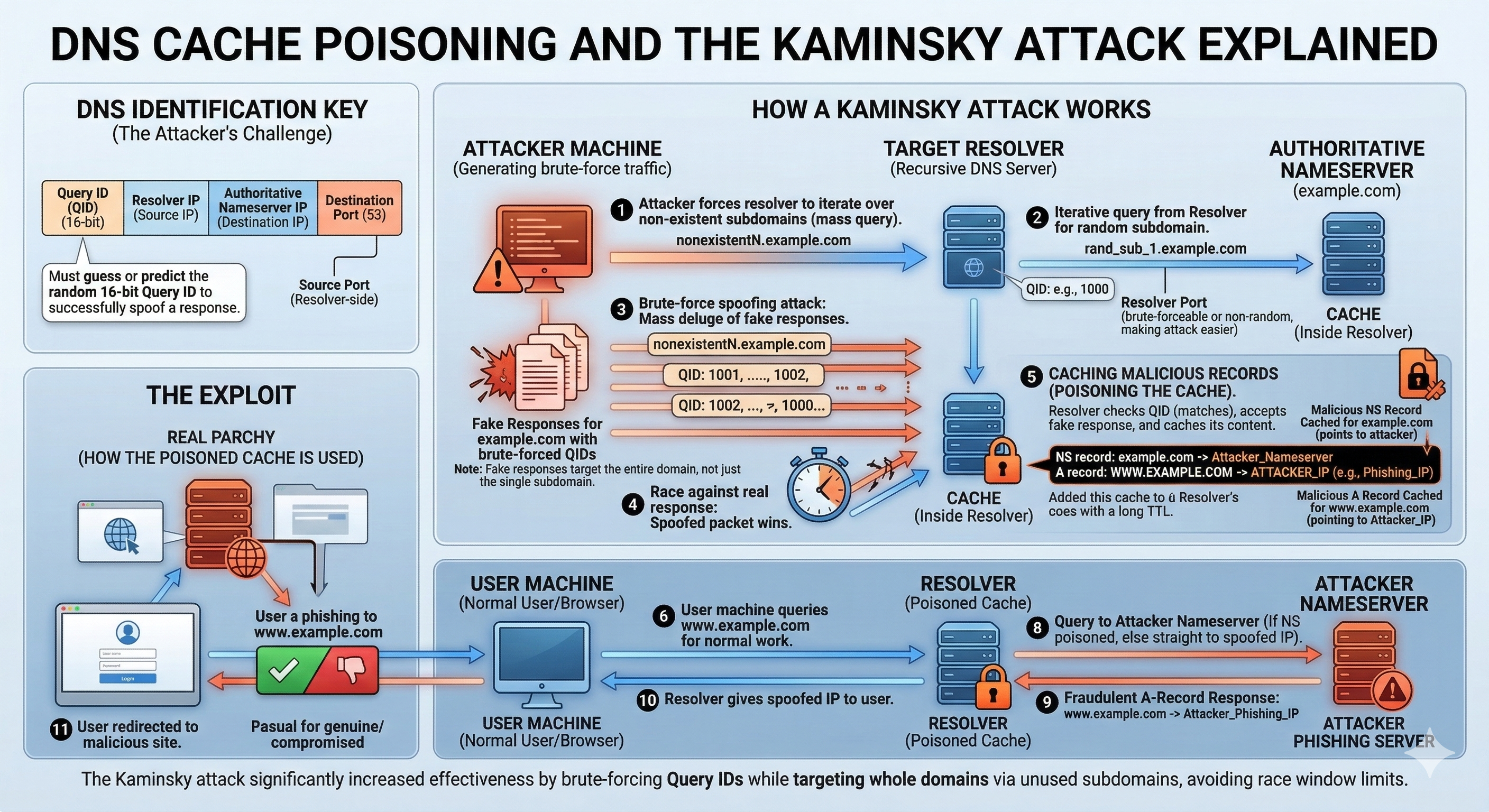
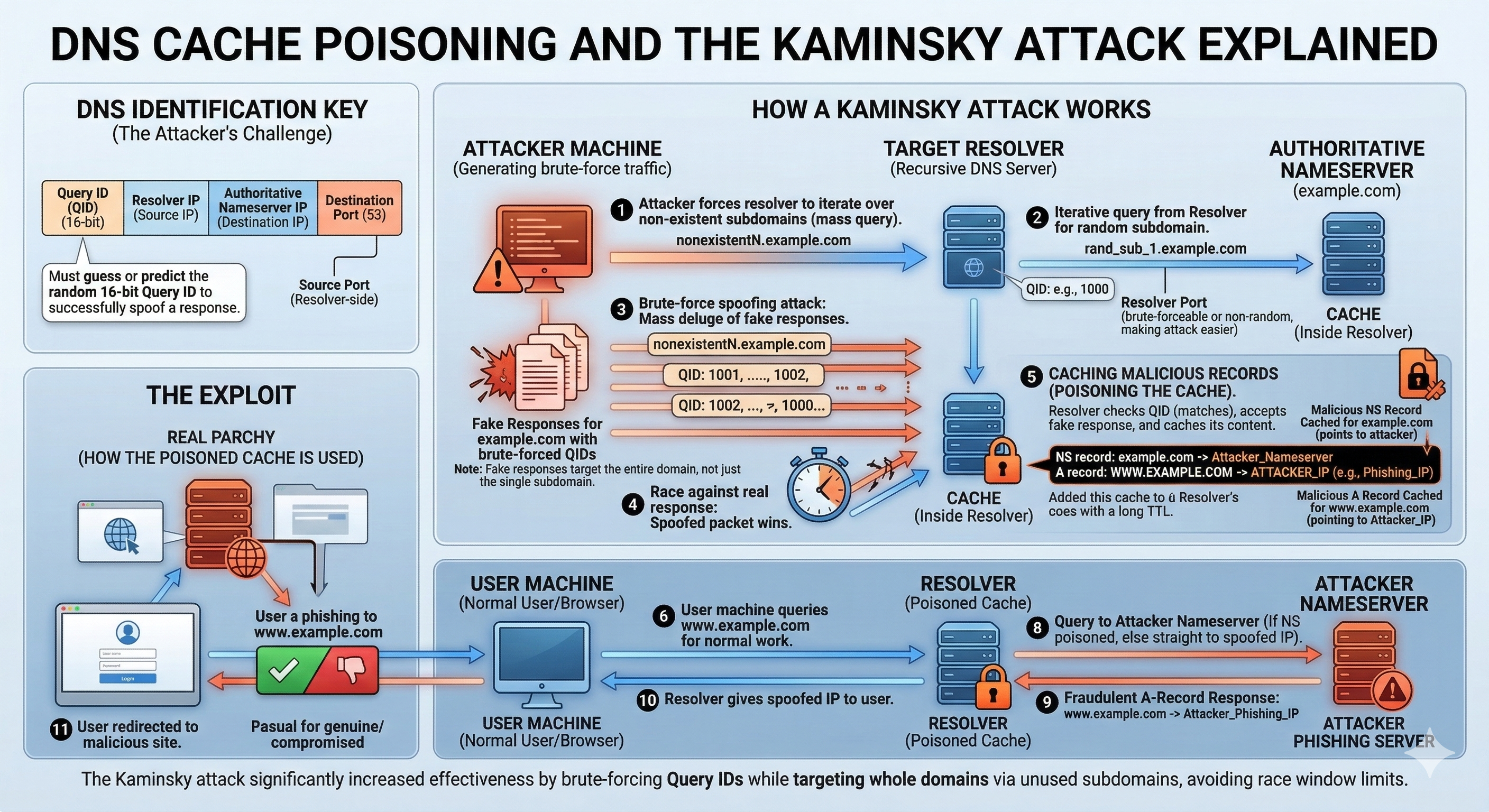
DNS cache poisoning is a cyberattack where an attacker inserts false DNS information into the cache of a recursive DNS resolver.
Once the malicious record is stored in the resolver’s cache, users who query the affected domain will receive the forged response instead of the legitimate one.
This allows attackers to redirect users to:
Because many users share the same recursive DNS resolver, a single successful cache poisoning attack can affect large numbers of users simultaneously.
DNS cache poisoning typically exploits weaknesses in how resolvers validate DNS responses.
A simplified attack sequence looks like this:
The poisoned entry remains active until its TTL (Time To Live) expires.
One of the most famous DNS vulnerabilities was discovered in 2008 by security researcher Dan Kaminsky.
The attack exploited weaknesses in DNS transaction ID prediction. By generating large numbers of spoofed responses, attackers could guess the correct transaction ID and inject forged DNS records into resolver caches.
This vulnerability affected a wide range of DNS servers and led to global security patches across the Internet.
The Kaminsky discovery fundamentally changed DNS security practices.
DNS cache poisoning can have severe consequences because DNS is used by nearly every Internet service.
Successful attacks can enable:
In enterprise or ISP environments, a poisoned recursive resolver could affect thousands or millions of users.
Modern DNS resolvers implement several defenses against cache poisoning attacks.
These mechanisms make it extremely difficult for attackers to successfully forge DNS responses.
The most robust protection against DNS cache poisoning is DNSSEC (DNS Security Extensions).
DNSSEC adds cryptographic signatures to DNS records. Recursive resolvers can validate these signatures to ensure the response was not altered in transit.
If a forged DNS response is received, the DNSSEC validation process will fail, and the resolver will reject the data.
This prevents attackers from injecting fake DNS records into resolver caches.
Modern DNS security platforms also provide additional protections against malicious domains and DNS-based attacks.
Examples include:
These systems help prevent users from reaching malicious infrastructure even if attackers attempt DNS manipulation.