What is DNS?
#
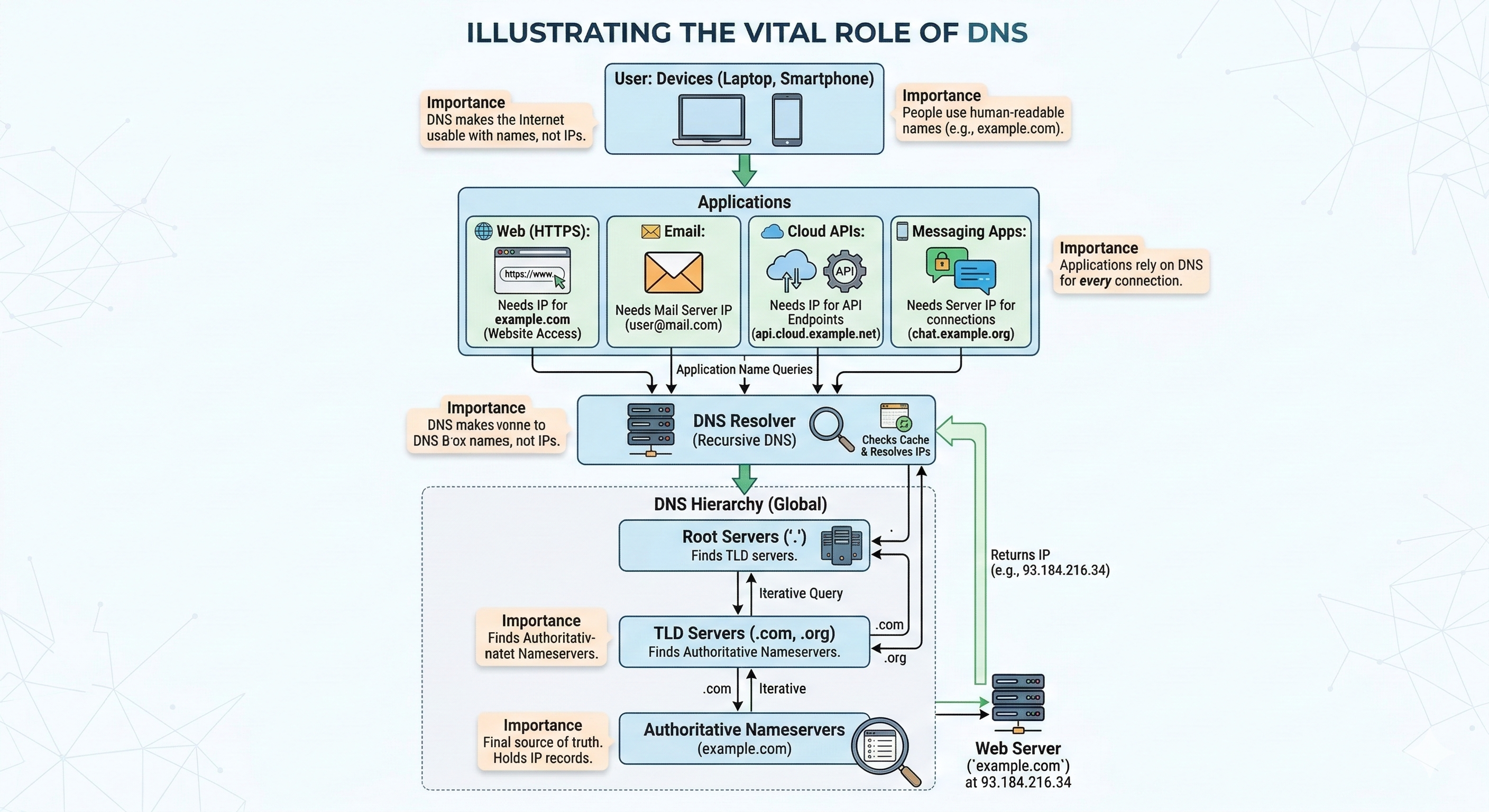
The Domain Name System (DNS) is the global distributed system that translates human-readable domain names into numerical IP addresses.
Computers communicate using IP addresses such as:
142.250.74.196
2001:4860:4860::8888
Because these numbers are difficult for humans to remember, DNS allows users to access Internet services using names like:
- google.com
- example.org
- planisys.net
When a user opens a website, sends an email, or connects to a cloud service, a DNS lookup occurs behind the scenes to determine the correct server address.
In practice, every digital interaction on the Internet begins with DNS.
DNS: A Foundational Internet Service
#
The Domain Name System is one of the most widely used yet least understood components of modern Internet infrastructure and cybersecurity.
Every digital interaction — opening a website, sending an email, connecting to a cloud service, or downloading a software update — starts with a DNS query.
Without DNS, practically no application or Internet service could function.
Web browsing, email delivery, APIs and cloud platforms all rely on DNS resolution to locate the systems that provide services.
Because of this universality, DNS has become both a critical operational dependency and a strategic control point for cybersecurity.
DNS as a Trusted Channel
#
This central role has led to a widespread operational mindset: DNS traffic must be allowed to flow freely.
Many network administrators hesitate to filter or inspect DNS traffic because they fear disrupting critical services.
As a result, DNS is often treated as a trusted protocol that passes through network security controls without inspection.
This default permissiveness creates a significant security blind spot.
Attackers increasingly exploit DNS as a communication channel for malicious activity including:
- command-and-control communication
- data exfiltration
- DNS tunneling
- phishing infrastructure
- malware domain resolution
Because DNS traffic is rarely blocked, adversaries frequently use it to bypass traditional security defenses.
How DNS Has Evolved
#
Over the past decade DNS has expanded far beyond its original role of translating names into IP addresses.
Today DNS supports a wide array of infrastructure functions including:
- Email authentication through SPF, DKIM and DMARC records
- Cloud infrastructure orchestration where providers like Amazon Route 53 combine authoritative DNS with traffic steering and global failover
- Service discovery and modern protocols such as HTTPS resource records, DNS-based Service Discovery (DNS-SD) and ENUM
- Infrastructure automation where DevOps teams integrate DNS management into tools like Terraform so DNS records evolve alongside cloud resources
How DNS Resolution Works
#
When a user accesses a website, the DNS resolution process follows several steps across the global DNS hierarchy.
- A user enters example.com in a browser.
- The device sends a query to a DNS resolver.
- The resolver checks its cache for the answer.
- If the answer is not cached, the resolver queries the root servers.
- The root servers return the TLD servers responsible for the domain.
- The resolver queries the TLD servers.
- The TLD servers return the authoritative nameservers for the domain.
- The resolver queries the authoritative server and obtains the IP address.
- The resolver returns the result to the client.
The DNS Hierarchy
#
DNS is organized as a hierarchical system that distributes responsibility across many organizations.
- Root servers – the starting point of DNS resolution
- Top Level Domain (TLD) servers – responsible for domains such as .com, .org and country code domains
- Authoritative servers – store the official DNS records for each domain
This distributed architecture allows DNS to scale to billions of queries per day while remaining resilient and decentralized.
Common DNS Record Types
#
- A – maps a domain to an IPv4 address
- AAAA – maps a domain to an IPv6 address
- MX – identifies email servers
- TXT – stores text information such as SPF, DKIM and verification tokens
- CNAME – defines an alias for another domain
- NS – specifies authoritative nameservers
DNS and Internet Security
#
Because DNS sits at the beginning of almost every Internet connection, it has become a critical security control point.
Modern DNS deployments often integrate security technologies such as:
- DNSSEC to protect the authenticity of DNS responses
- RPZ policy zones to block malicious domains
- encrypted DNS protocols such as DoT, DoH and DoQ
- Protective DNS services used by enterprises and Internet Service Providers
Understanding DNS is therefore essential not only for operating Internet infrastructure, but also for protecting modern networks against cyber threats.
Related DNS Topics