DANE Explained
E-mail tied to DNSSEC for better privacy and security, and to avoid spoofing
E-mail tied to DNSSEC for better privacy and security, and to avoid spoofing
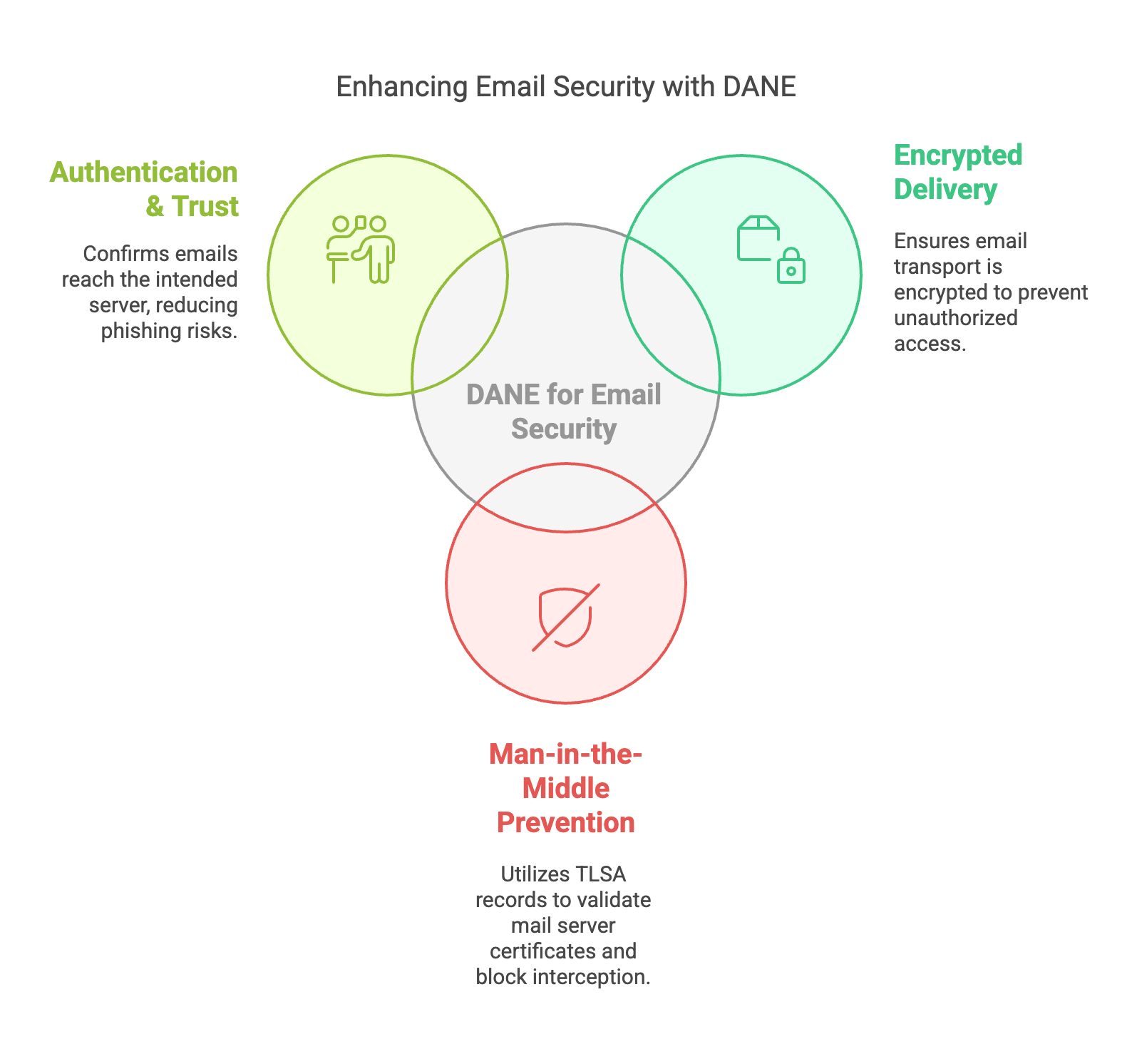
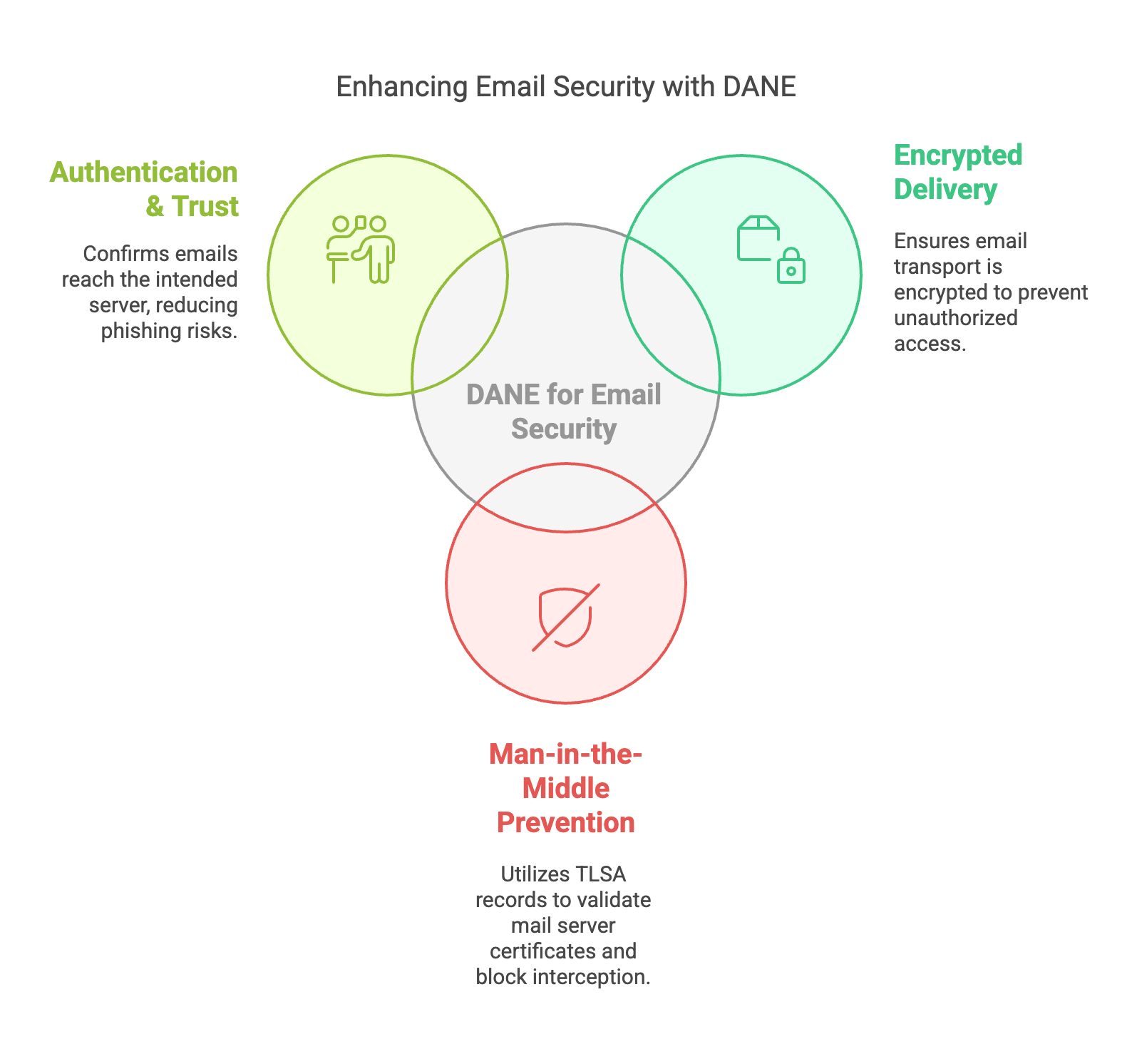
DANE (DNS-Based Authentication of Named Entities) uses DNSSEC to authenticate TLS certificates using TLSA records.
Postfix supports DANE (DNS-Based Authentication of Named Entities) to authenticate SMTP servers using DNSSEC-validated TLSA records. This allows mail servers to verify TLS certificates using DNSSEC instead of relying exclusively on traditional Certificate Authorities.
When DANE is enabled, Postfix will automatically check DNS for TLSA records associated with the destination mail server and validate them using DNSSEC. If the DNSSEC chain of trust is valid, the SMTP connection can be authenticated cryptographically.
# /etc/postfix/main.cf
smtp_tls_security_level = dane
smtp_dns_support_level = dnssec
smtp_tls_loglevel = 1
smtp_tls_CAfile = /etc/ssl/certs/ca-certificates.crt
smtp_tls_protocols = !SSLv2, !SSLv3
smtp_tls_mandatory_protocols = !SSLv2, !SSLv3
smtp_tls_mandatory_ciphers = high
smtp_tls_ciphers = high
A mail server supporting DANE publishes a TLSA record similar to the following:
_25._tcp.mail.example.com. IN TLSA 3 1 1 2A3F1D6E8E2F...
dig +dnssec _25._tcp.mail.example.com TLSA
If DNSSEC validation succeeds, a DANE-enabled SMTP server can use this information to authenticate the remote mail server before delivering email.