Malware Domains and DNS Attack Infrastructure
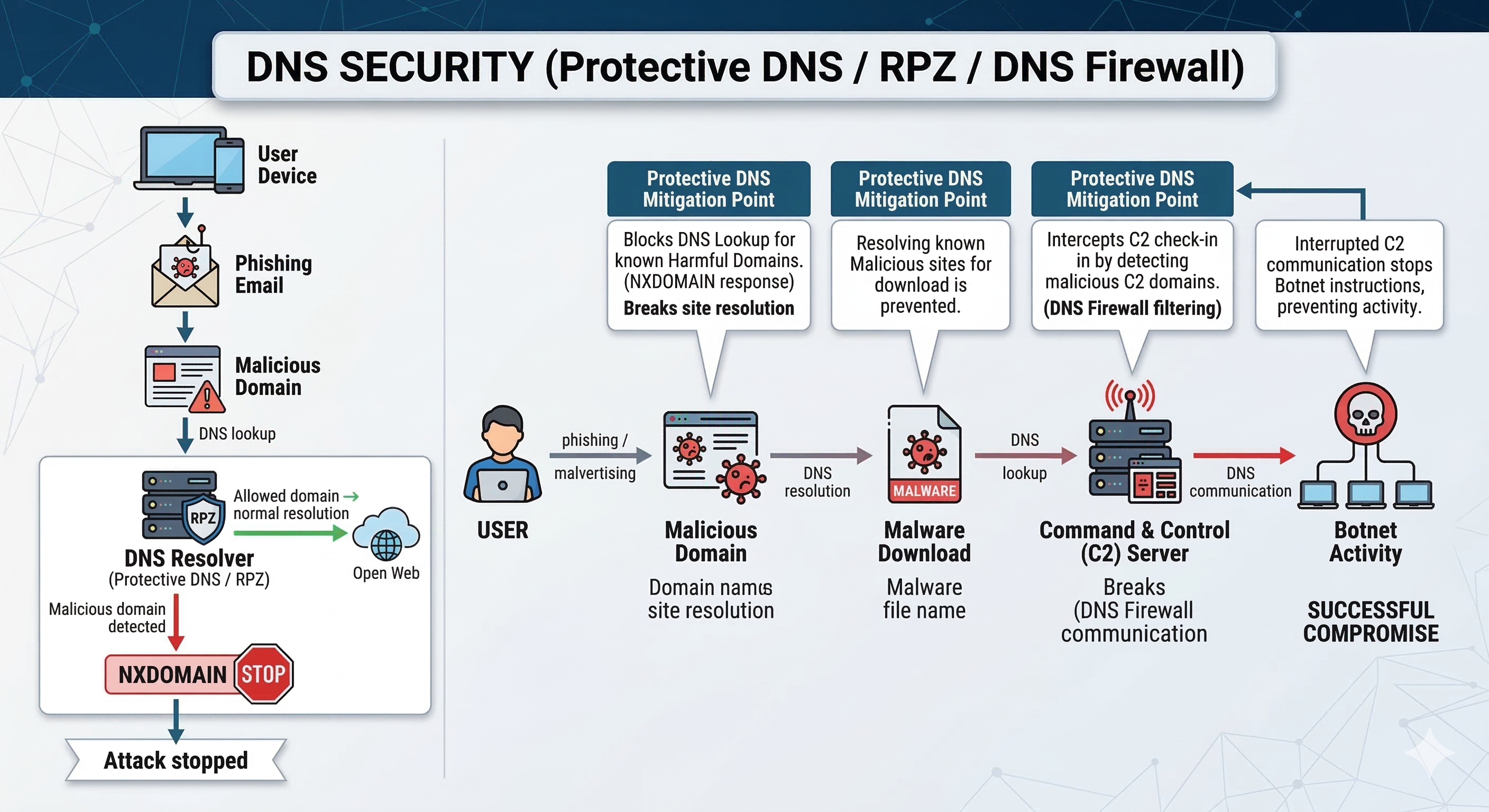
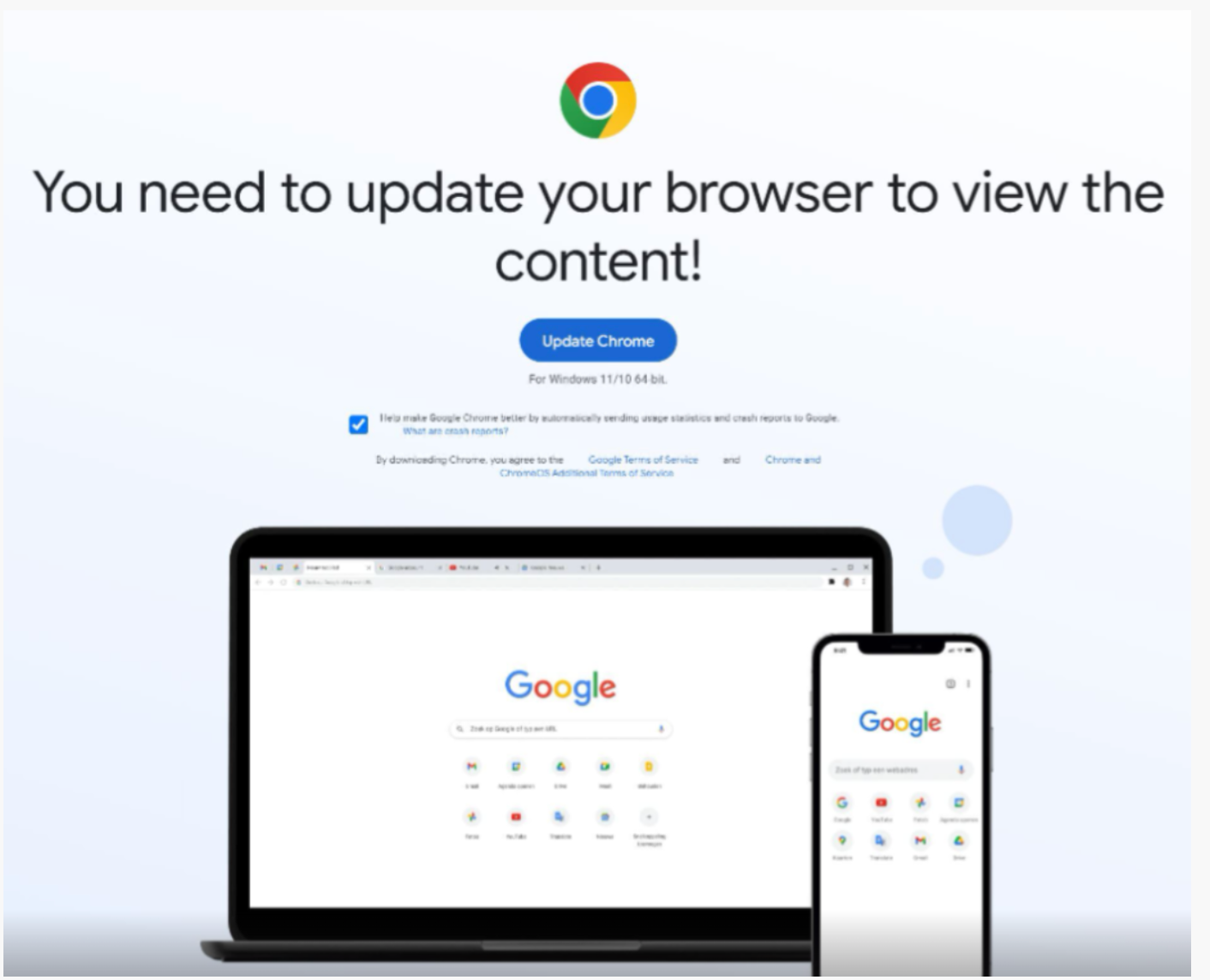
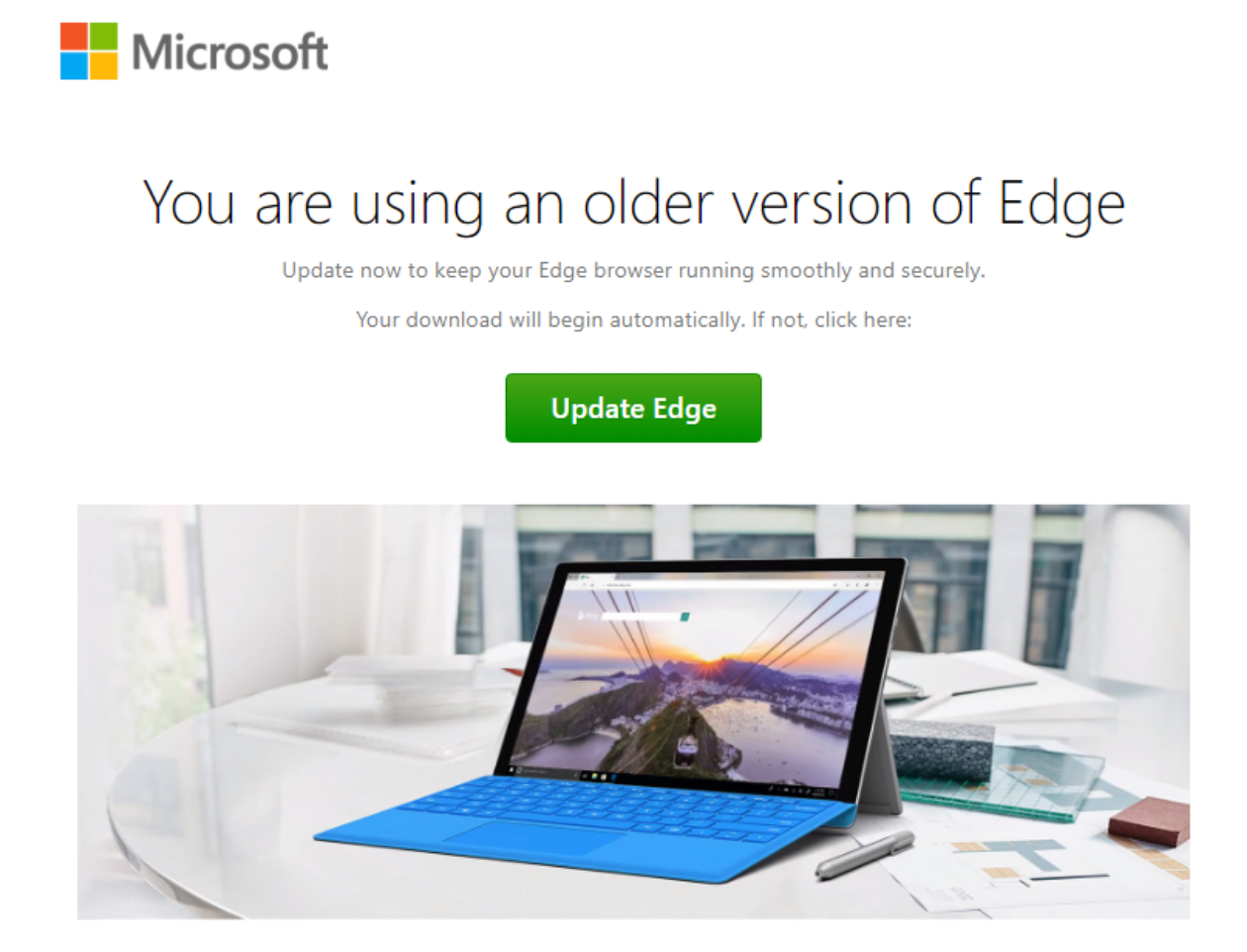
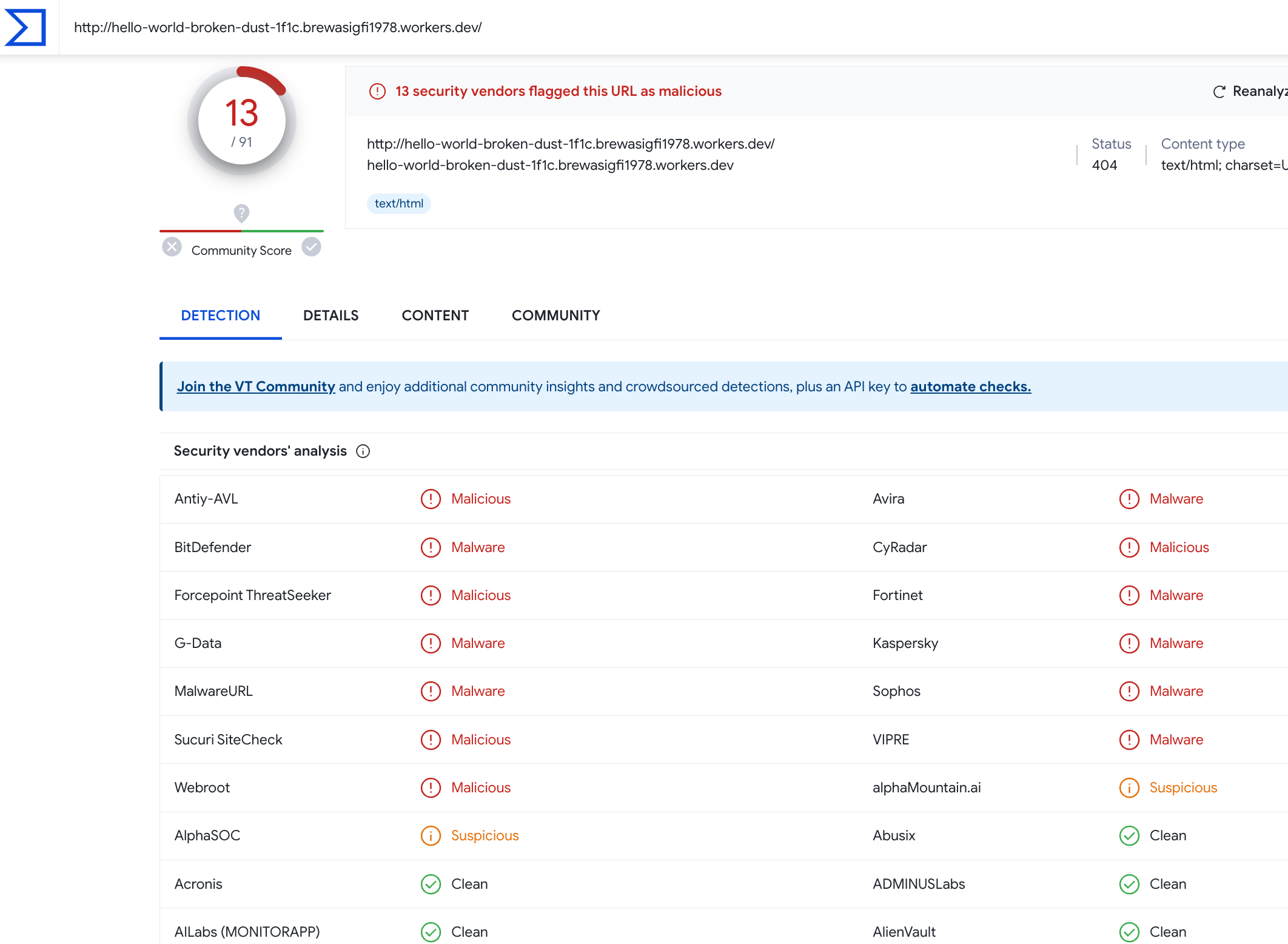
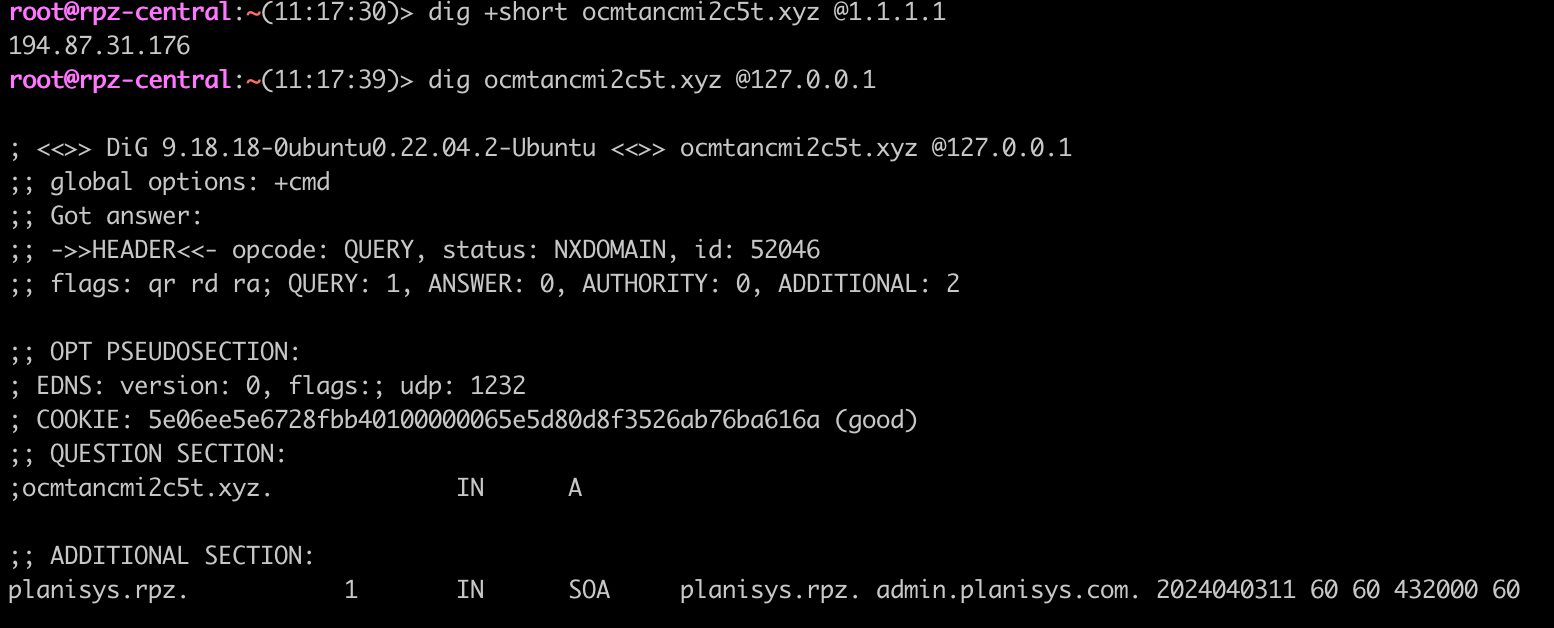
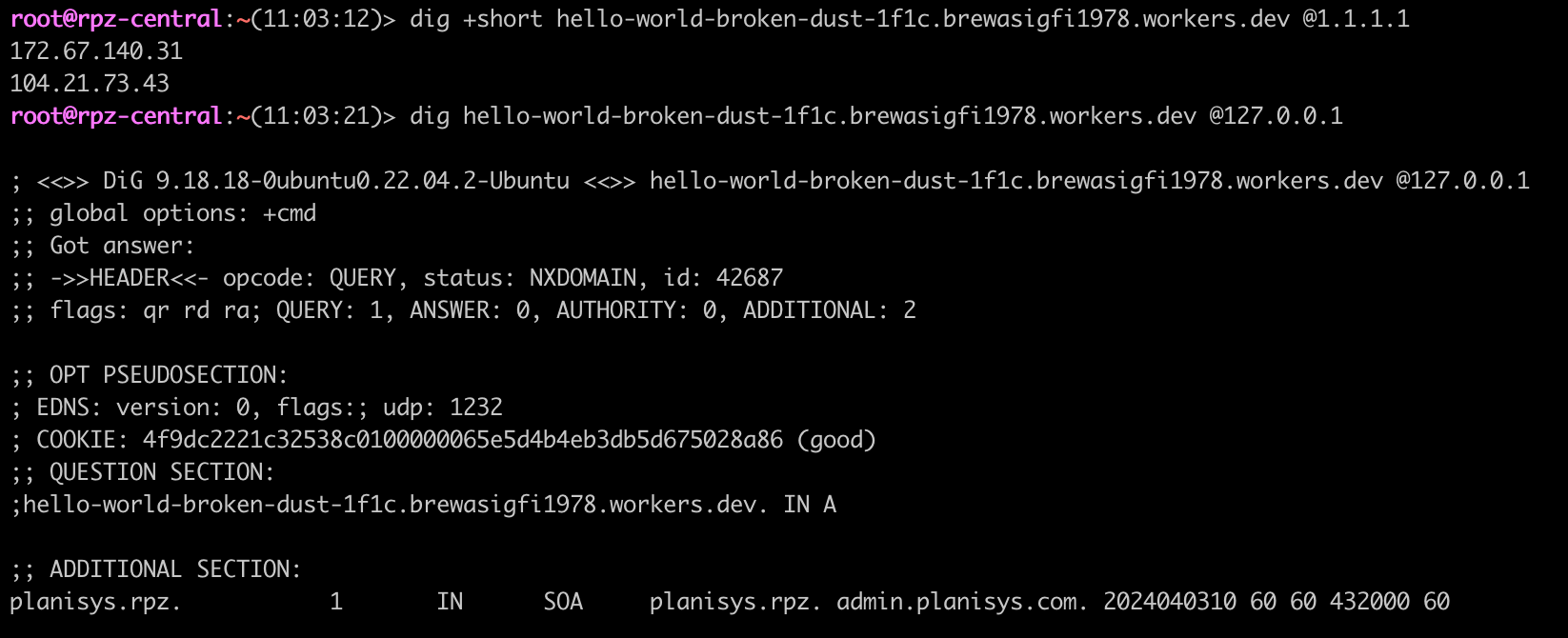
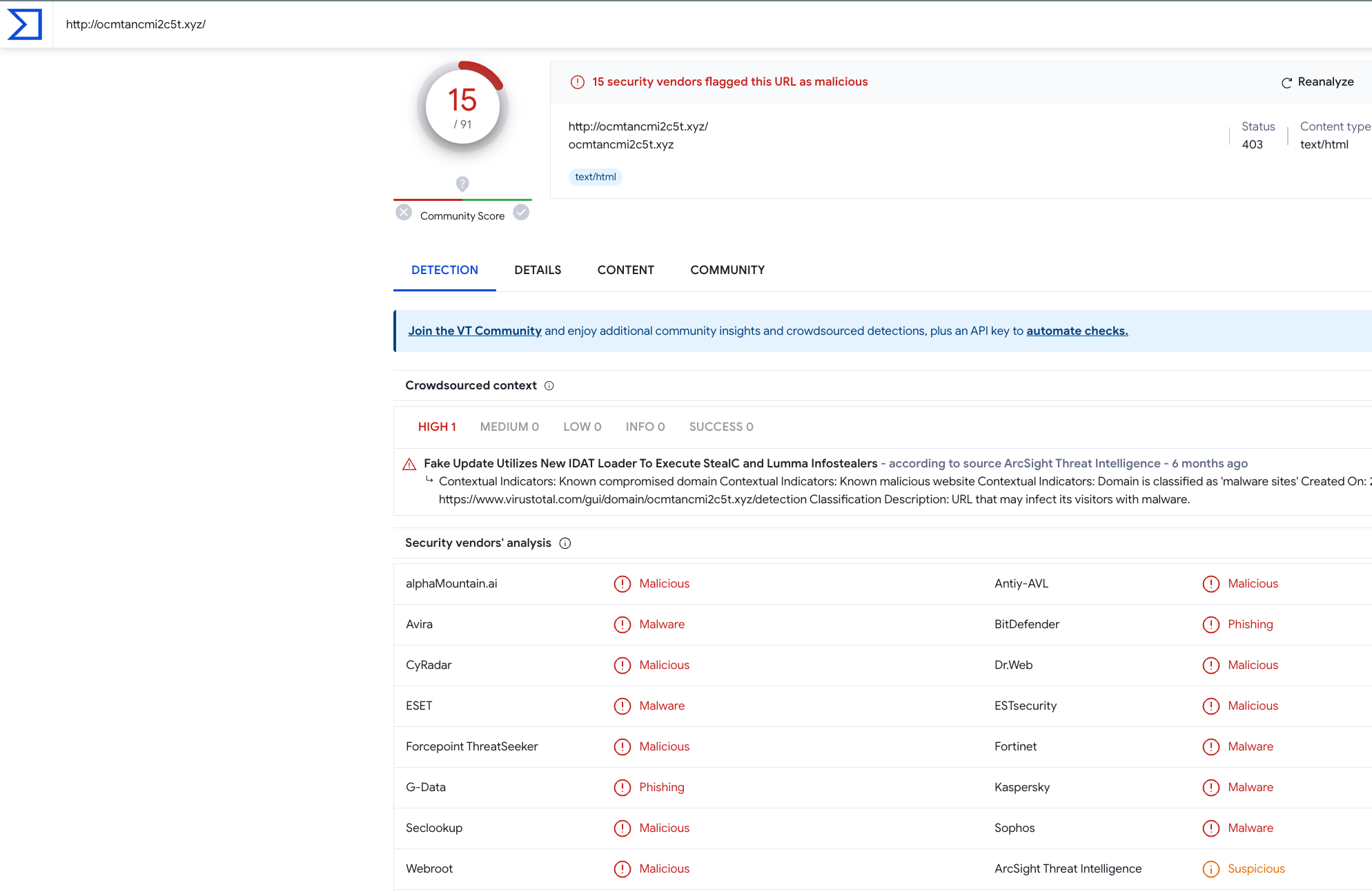
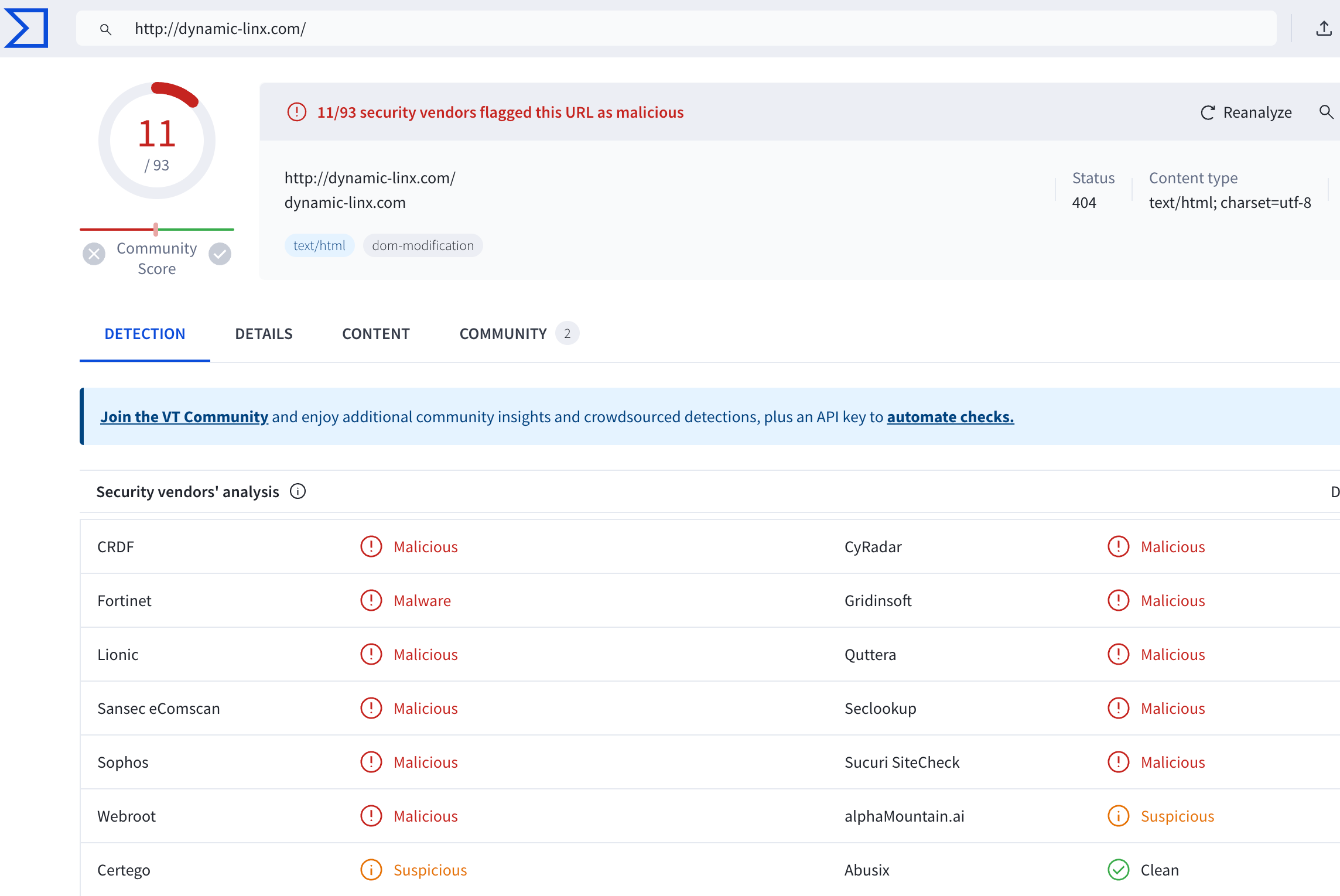
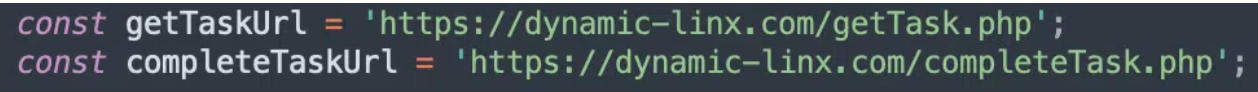
Many cyberattacks rely on DNS to locate malicious domains, download malware, and communicate with command-and-control servers. DNS firewalls can interrupt this attack chain by blocking domain resolution.