Why Malware Uses DNS
#
DNS is one of the most widely allowed protocols in corporate and ISP networks.
Almost every device must resolve domain names in order to communicate on the Internet.
Because DNS traffic is rarely blocked, malware authors frequently use DNS
as a communication channel between infected machines and attacker infrastructure.
This allows malware to:
- Locate command-and-control servers
- Download additional malware payloads
- Receive instructions from attackers
- Exfiltrate stolen data
DNS Command-and-Control Infrastructure
#
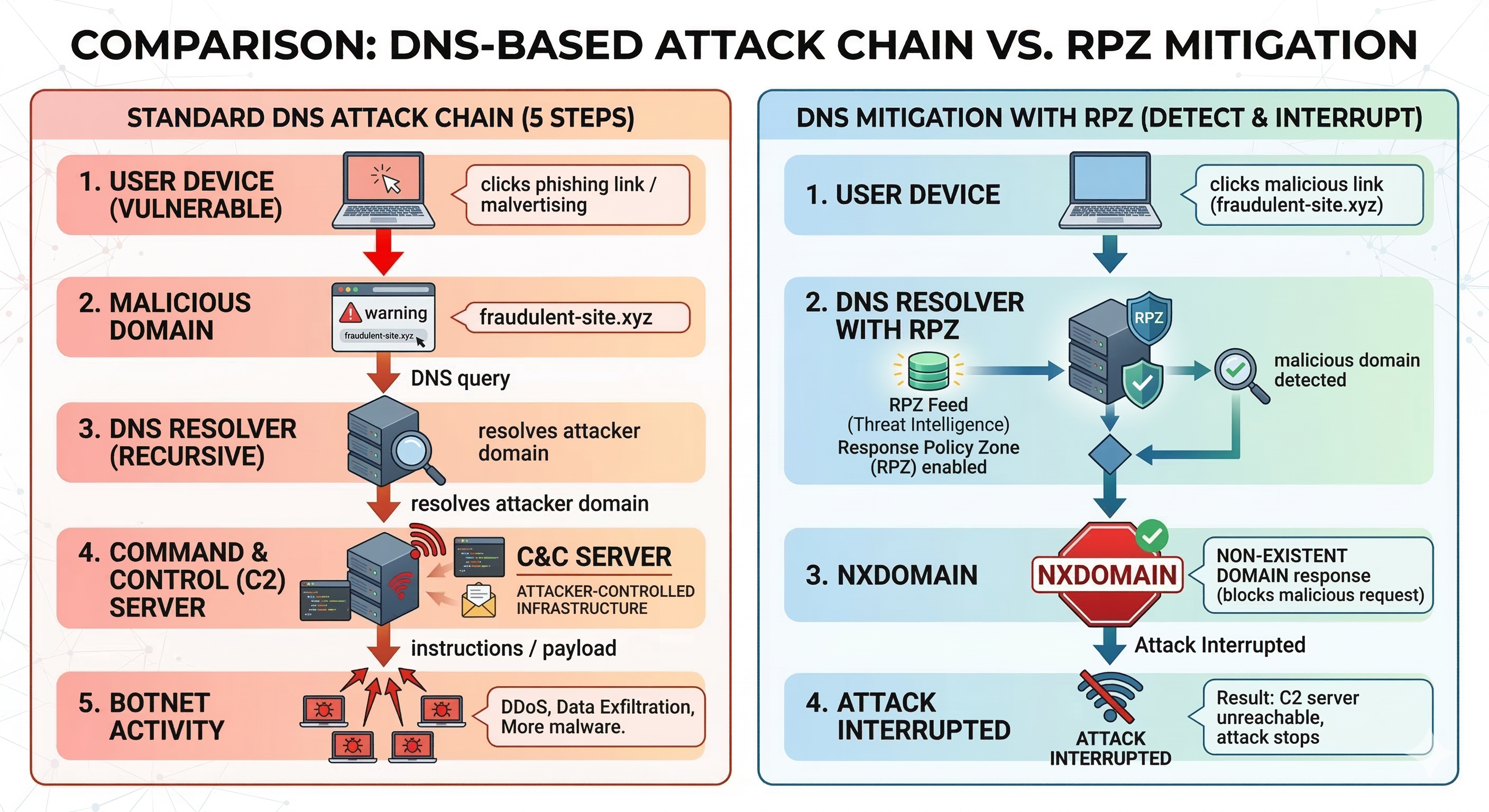
Most botnets rely on command-and-control (C2) servers to coordinate the activity
of infected machines. Instead of hardcoding IP addresses, malware often uses
domain names that can change over time.
An infected device typically performs DNS queries to locate the current
C2 server used by the botnet.
For example:
- Infected host queries: update-malware-control.example
- DNS resolver returns attacker-controlled IP
- Malware connects to the server and receives instructions
Domain Generation Algorithms (DGA)
#
Some malware families use Domain Generation Algorithms (DGA)
to generate large numbers of pseudo-random domain names every day.
Instead of relying on a single domain, infected machines generate
hundreds or thousands of potential domain names and attempt
to resolve them via DNS.
Attackers only need to register one of these domains to regain
control of the botnet.
DGA techniques make it difficult to disrupt malware infrastructure
using traditional domain takedowns.
DNS Data Exfiltration
#
Some advanced malware families also use DNS to exfiltrate data.
Because DNS queries can contain arbitrary subdomains,
malware can encode stolen information inside DNS requests.
For example:
encoded-data.attacker-domain.com
These DNS queries allow attackers to extract sensitive
information while avoiding traditional network monitoring systems.
How Protective DNS Stops Malware
#
Protective DNS systems can disrupt malware communication
by blocking malicious domains used by botnets and phishing campaigns.
Technologies such as Response Policy Zones (RPZ)
allow DNS resolvers to intercept queries and prevent infected
machines from reaching attacker infrastructure.
- Blocks malware command-and-control domains
- Stops phishing domain resolution
- Prevents malware downloads
- Interrupts botnet communication
Related DNS Security Topics