DNS over QUIC (DoQ) Explained
A modern encrypted DNS protocol designed for performance, privacy and network resilience.
A modern encrypted DNS protocol designed for performance, privacy and network resilience.
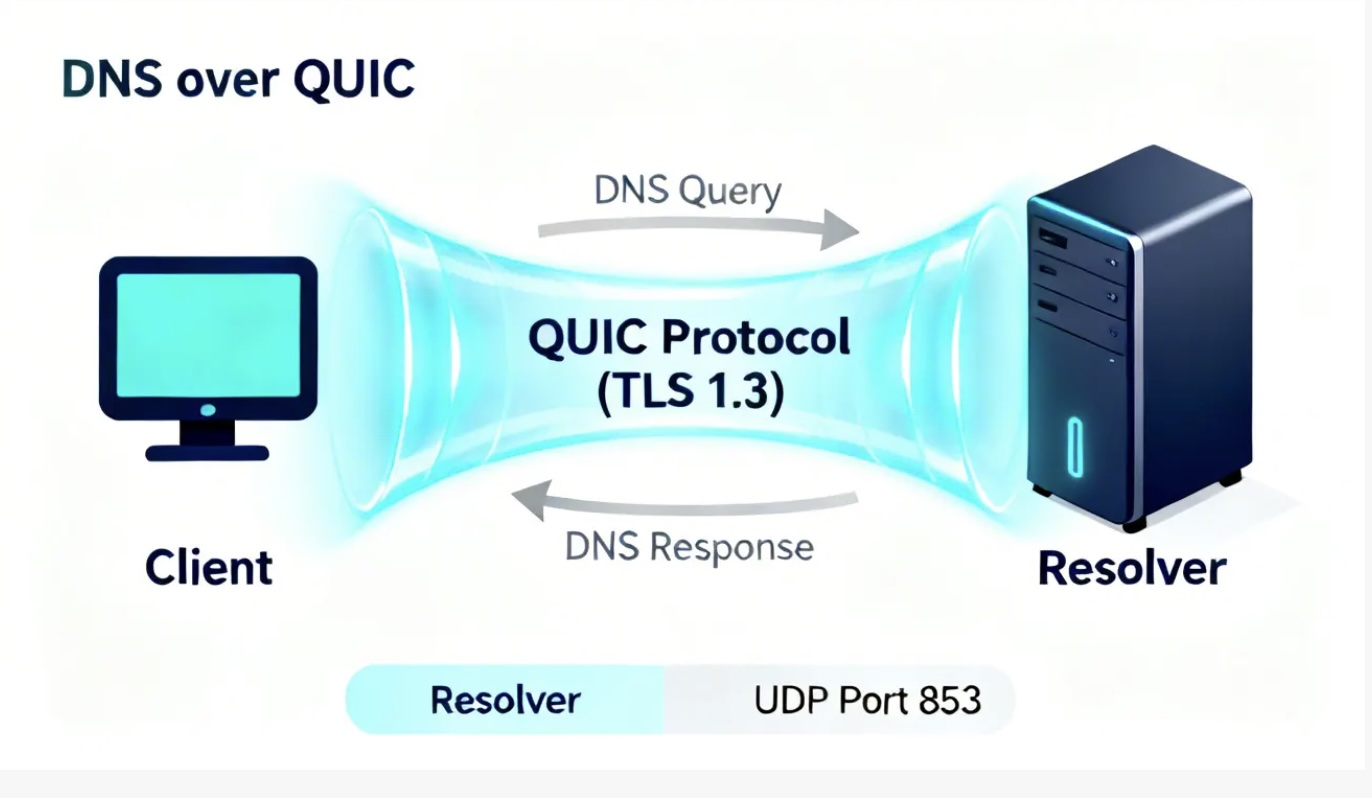
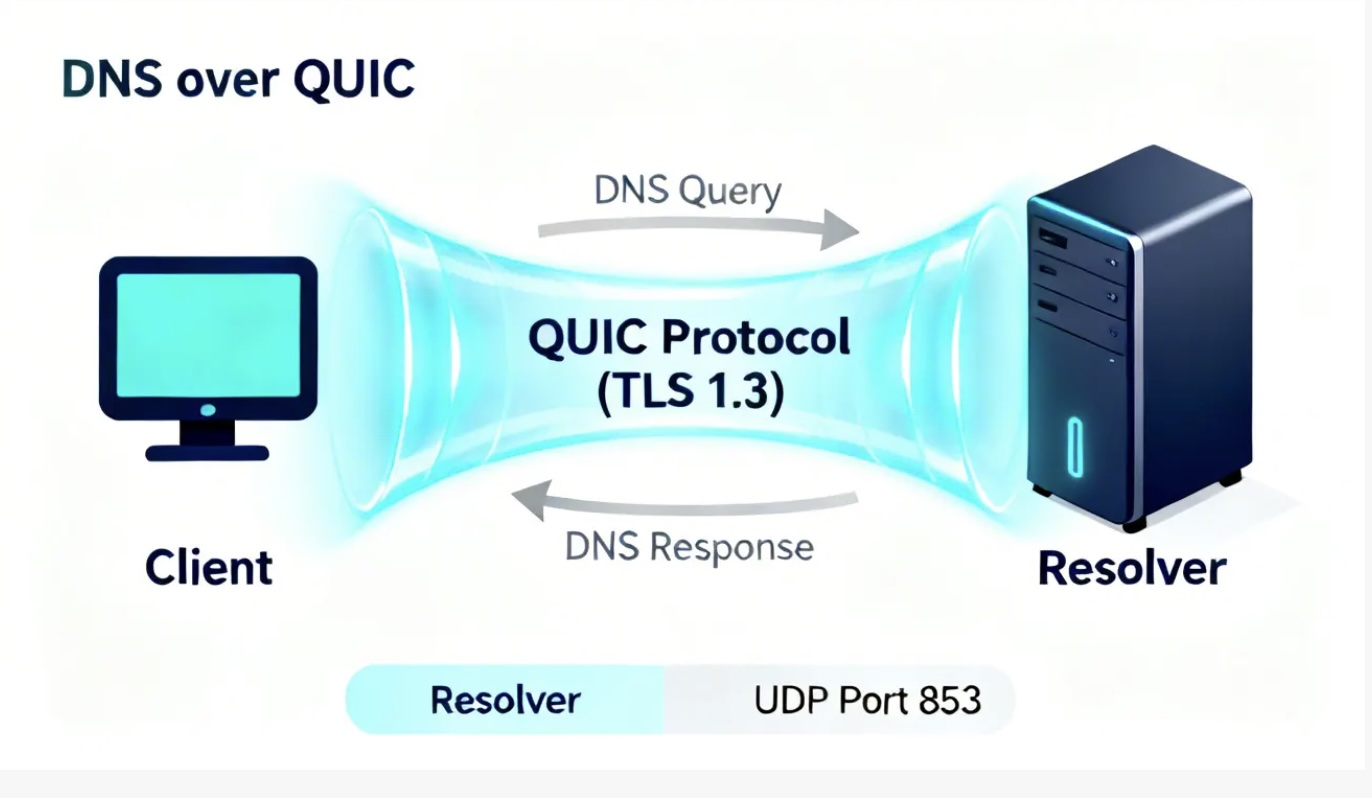
DNS over QUIC (DoQ) is an encrypted DNS transport protocol defined in RFC 9250 that protects DNS queries using the QUIC transport protocol, which incorporates TLS 1.3 encryption.
QUIC was originally developed by Google and later standardized by the IETF in RFC 9000. It was designed to improve Internet transport performance by reducing connection setup latency and improving behavior under packet loss.
Traditional DNS queries use UDP port 53 and are transmitted in clear text. This allows network operators, WiFi providers or attackers performing packet inspection to determine which domains users are accessing.
DNS over QUIC addresses this limitation by encrypting DNS traffic while also improving transport efficiency. Unlike TCP-based encrypted DNS protocols, DoQ minimizes handshake delays and improves DNS query performance.
In a typical deployment, a DNS client establishes an encrypted QUIC connection to a recursive resolver supporting DoQ.
Once established, multiple DNS queries can be transmitted through the same encrypted session without needing to renegotiate transport connections.
This model improves efficiency compared to traditional DNS where each query may require separate transport setup.
DNS is highly sensitive to latency. Even small improvements in connection establishment time can significantly impact user experience.
QUIC improves performance through:
Connection migration is particularly useful for mobile devices that move between WiFi and cellular networks without interrupting DNS sessions.
Traditional encrypted DNS such as DNS over TLS relies on TCP followed by TLS. This introduces additional latency due to sequential handshakes.
QUIC integrates transport and encryption into one protocol, allowing faster secure session establishment.
Both DoQ and DoH provide encrypted DNS, but their design goals differ.
DoH benefits from existing browser infrastructure while DoQ offers a more direct and efficient DNS transport without HTTP overhead.
| Protocol | Transport | Main advantage |
|---|---|---|
| DoT | TLS over TCP | Simple encrypted DNS |
| DoH | HTTPS | Browser compatibility |
| DoH3 | HTTP/3 over QUIC | Modern web transport |
| DoQ | QUIC native | Efficient DNS transport |
Modern DNS software can automatically discover encrypted DNS capabilities.
These discovery mechanisms allow clients to upgrade to encrypted DNS automatically when supported.
DoQ is increasingly relevant for:
Organizations deploying encrypted DNS often combine DoQ with DNS security platforms to ensure both privacy and protection.
Encrypted transport protects confidentiality but does not detect malicious domains.
DNS security platforms add threat protection through:
Combining encrypted DNS transport with DNS security enforcement provides both privacy and cybersecurity protection.
DNS protocol adoption typically evolves gradually.
DNS over TLS required several years to reach adoption while DNS over HTTPS spread faster due to browser integration.
DNS over QUIC benefits from the rapid global adoption of QUIC driven by HTTP/3 deployment across CDNs and Internet infrastructure.
While DNS over QUIC (DoQ) is defined in RFC 9250, many production DNS deployments do not yet implement QUIC directly inside their resolver. Instead, a common architecture separates the encrypted transport layer from the DNS resolution engine.
Modern deployments can implement DoQ by placing a QUIC-capable DNS proxy such as dnsdist in front of a BIND resolver. The proxy handles encrypted client connections while BIND continues to perform recursive resolution, RPZ filtering and DNS policy enforcement.
This architecture is enabled by the PROXYv2 protocol support added in BIND 9.20, which allows the original client IP address to be preserved when queries are forwarded from a proxy.
Without PROXYv2, the resolver would only see the proxy address instead of the real client. With PROXYv2 enabled, BIND receives the true client IP, allowing accurate logging, policy enforcement and threat analysis.
A typical architecture looks like this:
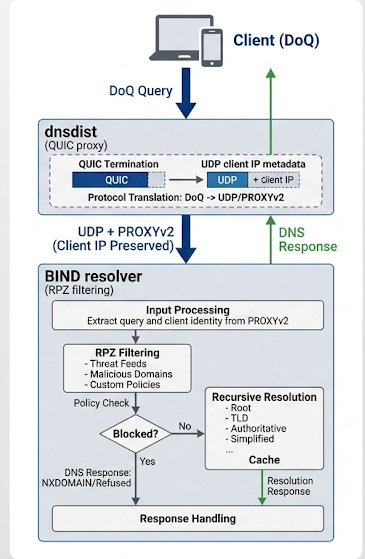
PROXYv2 preserves client identity for policy enforcement and logging
This design allows DNS operators to add support for modern encrypted transports such as DoQ, DoH and DoT without modifying the core resolver. It also improves operational flexibility by allowing the transport layer to evolve independently from the DNS engine.
This layered model is commonly used by large DNS security providers and Protective DNS platforms because it allows encrypted DNS transport, policy enforcement and DNS analytics to scale independently.
This architecture also allows multi-tenant DNS security platforms to support multiple encrypted DNS transports simultaneously while maintaining centralized policy enforcement.
Although DNS over QUIC offers clear technical advantages, its adoption is still emerging compared to DNS over HTTPS (DoH) and DNS over TLS (DoT).
One reason is that many widely deployed DNS resolvers such as BIND do not yet implement native QUIC support. Instead, operators typically deploy DoQ using a proxy architecture where a QUIC-capable frontend handles encrypted client sessions and forwards queries to an existing resolver.
Another factor is that DoH already provides encrypted DNS transport and has strong adoption due to browser support. Because DoH runs over HTTPS, it can reuse existing web infrastructure and client software, which accelerated its deployment.
DoQ adoption is therefore progressing gradually, similar to how DNS over TLS evolved after its standardization. New transports typically require time for client software, resolver implementations and operational experience to mature.
Despite this gradual adoption, DoQ is expected to become more important in environments where transport efficiency matters, including:
As QUIC continues to expand through HTTP/3 adoption, the ecosystem of libraries and networking tools supporting QUIC is growing rapidly, which is expected to accelerate DoQ deployment in the coming years.
The kdig utility supports DNS over QUIC testing.
kdig @1.1.1.1 example.com +quic
This sends a DNS query over QUIC instead of traditional UDP or TCP.
As of BIND 9.20 and current development versions, BIND does not natively implement DNS over QUIC. However, operators can deploy DoQ by placing a QUIC-capable DNS proxy such as dnsdist in front of a BIND resolver.
This architecture allows modern encrypted DNS transports while preserving BIND's recursive resolution, DNSSEC validation and RPZ security filtering.
DNS over QUIC and DNS over HTTPS both provide encrypted DNS transport. DoH benefits from browser integration while DoQ offers a more efficient transport designed specifically for DNS without HTTP overhead.
DoQ may provide performance advantages in high-latency or mobile networks, while DoH remains the most widely deployed encrypted DNS protocol today.
DNS over QUIC is most useful for organizations operating large resolver infrastructures such as ISPs, enterprises and DNS security providers. These environments benefit from QUIC features such as connection reuse, multiplexing and improved behavior under packet loss.
No. DNS over QUIC encrypts DNS transport but does not block malicious domains. DNS security requires additional technologies such as RPZ filtering, threat intelligence feeds and Protective DNS platforms.
DNS over QUIC adoption is still emerging. Some public DNS providers support DoQ, but most encrypted DNS traffic today still uses DNS over HTTPS. Adoption is expected to grow as QUIC becomes more widely deployed through HTTP/3 infrastructure.
Internet Service Providers are increasingly deploying encrypted DNS to protect users from DNS manipulation and surveillance. DNS over QUIC offers performance advantages compared to TCP-based encrypted DNS because it reduces connection overhead and improves performance in mobile and high-latency environments.
For large resolver deployments, QUIC can also reduce TCP connection state and improve scalability while maintaining strong encryption.
Yes. DNS over QUIC encrypts DNS transport while DNS filtering technologies such as RPZ and Protective DNS provide security enforcement.
Modern DNS security platforms typically combine encrypted DNS transports such as DoQ, DoH and DoT with DNS filtering policies to provide both privacy and threat protection.
Enterprise networks benefit from DNS over QUIC because it improves DNS privacy while maintaining performance. QUIC transport can also improve DNS reliability for remote workers and roaming devices that frequently change networks.
Organizations deploying DNS security platforms can use DoQ to protect DNS traffic between endpoints and resolvers while still enforcing centralized DNS security policies.